Monday, 31 March 2014
Labels:
Cyber News
Read More
Ary Digital official website got hacked
Official website of Ary Digital (Pakistan famous news channel) have been hacked and defaced by famous Pakistani Hacker group “Pakistan Haxor Crew”
Website was hacked by famous Pakistani Hacker “H4$N4!N H4XOR” . The reason of hacking of website is to give message.
Message :Our fight is not against any individual but the system as a whole.. Should you choose to ignore security, it will reincarnate as your worst nightmare ! We just defaced your website to give you a chance to put your hands on it before others come and destroy it
Hacked website and mirror :
Friday, 28 March 2014
Labels:
Cyber News
Read More
Windows XP open invitation to hacker's
The death of Windows XP is just days away, and experts say businesses that don’t upgrade are basically sending an open invitation to cybercriminals.
On April 8, Microsoft (MSFT, Fortune 500) will no longer provide security updates, or “patches,” for its Windows XP operating system. This means computers running on XP — and even machines like ATMs — will be largely unprotected against viruses and cyber attacks.
While Microsoft declined to disclose how many small businesses currently use Windows XP, Forrester Research estimates about 6% of companies’ PCs will still be using it by the April deadline. Experts say those are predominately small and medium-sized firms.
“A year ago, 35% of machines for our small business customers [about 1 million machines] were still on XP,” said Sergio Galindo, general manager with GFI Software, which provides IT support to small and mid-sized businesses. “I couldn’t believe it.” (That’s since dropped to about 23%.)
What does this mean for those businesses on April 9? Not a lot — at first, said Galindo. XP will keep working, and businesses that rely on it will keep functioning.
But the risks will compound over time.
“It’s like expired milk,” said Galindo. “If you drink it one day after it expires, you’re OK. But after a month, the risk is exponentially greater.”
The risk can’t be overstated, said Thomas Hansen, vice president of small and medium business at Microsoft (MSFT, Fortune 500). In fact, Microsoft’s own research has shown that Windows XP, released in 2001, is five times more susceptible to viruses and cyberattacks than Windows 8, its newest operating system.
Microsoft announced in September 2007 that it was planning to phase out Windows XP in order to give people plenty of time to prepare.
“The world and technology has moved on,” said Hansen. “This is a decade-old technology that doesn’t fit in the modern world.”
Eric Marcus has seen both sides of the issue. His IT firm, Marcus Networking in Tempe, Ariz., caters to small and medium-sized businesses and has updated more than 1,400 workstations in the last five months.
He also spent $20,000 replacing 15 laptops at his own business with machines that run Windows 7.
It’s a cost he budgeted for, but many of his clients have struggled with the expense. “They have to pay for new equipment and our time. It adds up,” he said.
And some businesses, he’s discovered, run proprietary programs that are only compatible with XP.
Microsoft’s Hansen said the company is aware of that problem. “We don’t have the perfect answer yet on how to solve that situation,” he said....
Wednesday, 26 March 2014
Labels:
Cyber News
Read More
CASH! CASH! Hacking ATM Machines with Just a Text Message
As we reported earlier, Microsoft will stop supporting the Windows XP operating system after 8th April, apparently 95% of the world’s 3 million ATM machines are run on it. Microsoft's decision to withdraw support for Windows XP poses critical security threat to the economic infrastructure worldwide.
MORE REASONS TO UPGRADE!!!
Security researchers at Antivirus firm Symantec claimed that hackers can exploit a weakness in Windows XP based ATMs, that allow them to withdraw cash simply by sending an SMS to compromised ATMs.
"What was interesting about this variant of Ploutus was that it allowed cybercriminals to simply send an SMS to the compromised ATM, then walk up and collect the dispensed cash. It may seem incredible, but this technique is being used in a number of places across the world at this time." researchers said.
HARDWIRED Malware for ATMs
According to researchers - In 2013, they detected a malware named Backdoor.Ploutus, installed on ATMs in Mexico, which is designed to rob a certain type of standalone ATM with just the text messages.
To install the malware into ATMs machines, hacker must connect the ATM to a mobile phone via USB tethering and then to initiate a shared Internet connection, which then can be used to send specific SMS commands to the phone attached or hardwired inside the ATM.
"Since the phone is connected to the ATM through the USB port, the phone also draws power from the connection, which charges the phone battery. As a result, the phone will remain powered up indefinitely."
HOW-TO HACK ATMs
- Connect a mobile phone to the machine with a USB cable and install Ploutus Malware.
- The attacker sends two SMS messages to the mobile phone inside the ATM.
- SMS 1 contains a valid activation ID to activate the malware
- SMS 2 contains a valid dispense command to get the money out
- Mobile attached inside the ATM detects valid incoming SMS messages and forwards them to the ATM as a TCP or UDP packet.
- Network packet monitor (NPM) module coded in the malware receives the TCP/UDP packet and if it contains a valid command, it will execute Ploutus
- Amount for Cash withdrawal is pre-configured inside the malware
- Finally, the hacker can collect cash from the hacked ATM machine.
Researchers have detected few more advanced variants of this malware, some attempts to steal customer card and PIN data, while others attempt man-in-the-middle attacks.
This malware is now spreading to other countries, so you are recommended to pay extra attention and remain cautious while using an ATM....
Monday, 24 March 2014
Labels:
Cyber News
Read More
A New Open Source Programming Language developed by Facebook
Facebook just released a new programming language called 'HACK', designed to build complex websites and other software quickly and without many flaws. The company has already migrated almost all of its PHP-based social networking site to HACK over the last year, but it has nothing to do with Hacking.
When Social Networking website Facebook was started 10 years ago, it was coded in PHP by Mark Zuckerberg and team, but as the company grew, PHP Programming platform became difficult to manage and bug-free.
Thus, Hack was born! Facebook Team decides to develop a new programming language that could combine elements of static-type programming languages such as C or C++ with dynamic-type languages like PHP, now called "HACK Programming Language".
"Hack has deep roots in PHP. In fact, most PHP files are already valid Hack files." Facebook said, "We have also added many new features that we believe will help make developers more productive."
HACK is a new version of PHP, requires Facebook’s HHVM (Hip Hop Virtual Machine) which is designed to execute programs written in Hack and PHP. The top 20 open source frameworks on Github run on HHVM.
"Traditionally, dynamically typed languages allow for rapid development, but sacrifice the ability to catch errors early and introspect code quickly, particularly on larger codebases." Facebook posted on itsengineering blog.
So Hack Programming Language offers a lot of potential for developers, enabling them to program faster and be able to catch errors more easily, among other things. "Conversely, statically typed languages provide more of a safety net, but often at the cost of quick iteration. We believed there had to be a sweet spot."
Beta code is open source and now available at Hacklang.org and you can also get Hack programming language tutorials from website to learn this new language. ...
"This is just the first step, and we are dedicated to continuing to evolve this software to make development even easier for both our own engineers and the broader community." The public release is not just to encourage developers, but also to quickly spot errors in Hack....
Sunday, 23 March 2014
Labels:
Cyber News

Read More
NSA Hacked Servers of Chinese telecom Huawei, Stole Source Codes.

The US Government was publicly accusing Chinese electronics manufacturer Huawei of espionage from the past few years.
Ironically, it has now been revealed that the National Security Agency conducted a major offensive cyber operations against the Chinese government and networking company Huawei, in early 2009.
According to reports based on classified documents leaked by Edward Snowden and viewed by The Times and Der Spiegel, NSA has infiltrated servers in the headquarters of Chinese telecommunications and hacked into the email servers of Huawei five years ago.
Code-named as "Operation Shotgiant" was conducted with the involvement of the CIA, White House intelligence coordinator and the FBI; aimed to find a link between Huawei and China’s People’s Liberation Army. NSA accessed the emails of many Huawei employees' for this purpose.
NSA STOLE SOURCE CODES
NSA also aimed to conduct surveillance through computer and telephone networks Huawei sold to other nations. According to the papers, NSA stole the secret source code for certain Huawei products, and obtained the information on how to exploit Huawei's products in order to spy on foreign customers such as Iran, Afghanistan, Pakistan, Kenya, and Cuba.
The reports show the NSA spying on former Chinese President Hu Jintao, the country’s trade ministry, banks, telecoms firms and also tracking more than 20 Chinese hacking groups, where more than half of them Chinese Army or Navy units.
"If it is true, the irony is that exactly what they are doing to us is what they have always charged that the Chinese are doing through us," William Plummer, a senior Huawei executive in the United States "If such espionage has been truly conducted, then it is known that the company is independent and has no unusual ties to any government and that knowledge should be relayed publicly to put an end to an era of mis- and disinformation."
NSA- 'WE HACK FOR NATIONAL SECURITY'
The US and China are hacking each other from long time and NSA spokeswoman Caitlin Hayden said that the NSA spying is for national security purposes only, "We do not give intelligence we collect to US companies to enhance their international competitiveness or increase their bottom line."
The US Government labeled their actions (Stealing Source codes, installing backdoors) as 'Hacking for National Security' and accusing Huawei for 'Corporate Theft'. In a document NSA wrote, "We currently have good access and so much data that we don't know what to do with it,"
Saturday, 22 March 2014
Labels:
Cyber News

Read More
Pileup flaw Android updates can be exploited by malware to gain permissions

Upgrading an operating system patches the security holes in the previous versions. However, researchers found a bug in upgrading process of Android itself, which can be exploited by malicious apps.
Sponsored Links
A team of researchers from Indiana University and Microsoft have published a paper explains a new critical security bugs which are referred as "Pileup flaws". The vulnerability exists in Package Management Service (PMS) of Android.
When a user upgrades android to the latest version, a malicious app with few or no permission in the old version can exploit this vulnerability to update itself with new set of permissions.
An attacker can exploit this vulnerability to steal sensitive information from the compromised device, change security configurations and also prevent installation of critical system services.
Researchers say they have confirmed the presence of security hole on all official android versions as well as 3,000 customized android versions.
Researchers also have developed a new service called 'SecUp' which is capable of detecting the malicious apps designed to exploit PileUp vulnerabilities...
Friday, 21 March 2014
Labels:
Cyber News
Read More
Scammers targeting Google Account with Phishing Page hosted on Google Drive
You all are quite aware of phishing attacks, and for those who are not, Phishing scams are typically fraudulent email messages, masquerading as a well known and trustworthy entity in an attempt to gather personal and financial information from victims. However, phishing attacks have become more sophisticated recently.
The Pro-hacker group, Syrian Electronic Army (SEA) is also popular for its advance phishing attack and had purposely targeted twitter account and websites of various popular brands like Forbes, Microsoft, Obama, Facebook, CNN, eBay and PayPal in the past using phishing techniques.
Security researchers have seen an increase in the number of phishing attacks every day, but recently a tricky scam came across by the researchers at the Symantec, which is targeting Google Docs and Google Drive users.
Under this phishing scam, an email with a subject of "Documents", tricks recipient to view an ‘important document’ stored on the Google Docs by clicking the included link in the email. But supposed to be directed to important Google doc, the user is redirected to a fake login page, where he is required to enter his Google account information, i.e. Username and Password.
One just needs to create a folder on Google Drive to host the phishing site, so it shows the address bar of the browser to “google.com” and let the fake login page run on the preview function of Docs. This allows criminals to make use of SSL encryption of Google, to deceive the victim further.
"The fake page is actually hosted on Google's servers and is served over SSL, making the page even more convincing," Symantec security expert Nick Johnston explained. "The scammers have simply created a folder inside a Google Drive account, marked it as public, uploaded a file there, and then used Google Drive's preview feature to get a publicly accessible URL to include in their messages."
It's really very common for the users to be prompted with a login page like this when accessing a Google Docs link and many of us may enter our credentials without a second thought. But, as soon as you enter the information and press "Sign in" button, a compromised web server with PHP script will receive and store your stolen credentials.
“This page then redirects to a real Google Docs document, making the whole attack very convincing. Google accounts are a valuable target for phishers, as they can be used to access many services including Gmail and Google Play, which can be used to purchase Android applications and content,” Johnston explained.
It is always recommended to login to any of your online accounts by entering the address into your browser's address bar rather than clicking a link in an unsolicited email and when any service required your login, have a close look that whether the request to click the link really makes sense or not.
Labels:
Cyber News
Read More
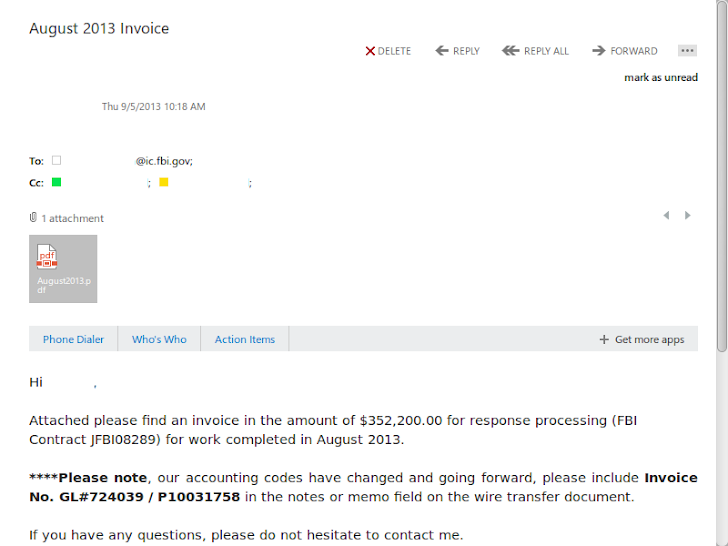
Microsoft sells your Information to FBI; Syrian Electronic Army leaks Invoices
Till now we all were aware about the truth that tech companies gave legal access to user data on the government's request, but we were unaware that well known tech companies also charge the government for providing data.
Syrian Electronic Army (SEA), the pro-hacker group, who had compromised Microsoft's Twitter account and blog, earlier this year and Microsoft did announce a breach on its blog earlier this year. "It appears that documents associated with law enforcement inquiries were stolen,".
It seems that they have achieved something bigger than we expected by once more targeting Microsoft.
This time the SEA hacking group has managed to successfully get into the FBI's super-secret Digital Intercept Technology Unit (DITU), where they found the actual invoices from Microsoft; detailing how much each request for data cost, which means that the company charges for every document they provide to the FBI agents, Daily Dot reported.
The invoices above shows that Microsoft charged the DITU $145,100 in December 2012, at a rate of $100 per data request. In August 2013, the per-request rate increased to $200 and the latest Invoice dated November 2013, showed a charge of $281,000.
These documents show how frequently the government calls on tech companies for information and could be possible that Microsoft isn't the only company that charges the government for compliance with data requests.
The group aligned with president Bashar al-Assad, is popular for targeting western countries and media and had victimized various high-profile brands and VIPs’ twitter accounts and websites, like Forbes, Obama, Facebook, CNN, eBay and PayPal in the past using phishing techniques, and recently claimed to compromise central repository of US central command (CENTCOM).
Thursday, 20 March 2014
Labels:
Cyber News

Read More
Google Glass malware developed by researchers
Google Glass malware developed by researchers
Forbes reports that two grad students at California Polytechnic San Luis Obispo recently developed POC spyware for Google Glass ).
Malware has been desighned by Mike Lady 22 year old researcher along with Kim Paterson 24 year old software professional , malware is able to take and upload photo every 10 seconds, without knowing a user.
Paterson said:- "The scary thing for us is that while it’s a policy that you can’t turn off the display when you use the camera, there’s nothing that actually prevents you from doing it,As someone who owns Glass and wants to install more apps, I’d feel a lot better if it were simply impossible to do that. Policies don’t really protect us."
Wednesday, 19 March 2014
Labels:
Cyber News
German Car Manufacture Company namely Citroen got hacked by some Unknown hackers,Hackers had planted a "Phishing Page" at shop.citroen.de inorder to get customers data and which lead to DATA COMPROMISATION.The Car makers have confirmed the "USER DATA COMPROMISE" occurs,but it’s uncount in how many quantity of CUSTOMERS are impacted.
Alex Holden of Hold Security has investigated the breach.The backdoor is now successfully removed according to there officials that backdoor was planted since 2013.
Hackers exploited Adobe Coldfusion vulnerability to get access on the server and customers data,
other renown website which are exploited by the same vulnerability in past were Smucker and SecurePay.
Source : http://www.whogothacked.com/2014/03/citroen-gets-hacked-customer.html
Read More
Citroen Deutschland Hacked Users Data Compromised
German Car Manufacture Company namely Citroen got hacked by some Unknown hackers,Hackers had planted a "Phishing Page" at shop.citroen.de inorder to get customers data and which lead to DATA COMPROMISATION.The Car makers have confirmed the "USER DATA COMPROMISE" occurs,but it’s uncount in how many quantity of CUSTOMERS are impacted.
Alex Holden of Hold Security has investigated the breach.The backdoor is now successfully removed according to there officials that backdoor was planted since 2013.
Hackers exploited Adobe Coldfusion vulnerability to get access on the server and customers data,
other renown website which are exploited by the same vulnerability in past were Smucker and SecurePay.
Source : http://www.whogothacked.com/2014/03/citroen-gets-hacked-customer.html
Tuesday, 18 March 2014
Labels:
Tutorials
Read More
Hacking Facebook User 'Access Token' with Man-in-the-Middle Attack
Facebook has several security measures to protect users' account, such as a user "access token" is granted to the Facebook application (like Candy Crush Saga, Lexulous Word Game), when the user authorizes it, it provides temporary and secure access to Facebook APIs.
To make this possible, users have to 'allow or accept' the application request so that an app can access your account information with the required permissions.
The Access Token stores information about permissions that have been granted as well as information about when the token will expire and which app generated it. Approved Facebook apps can publish or delete content on your behalf using the access tokens, rather than your Facebook password.
Access tokens are pretty sensitive, because anyone who knows the access token of a user can access the user's data and can perform any actions on behalf of the user, till the token is valid.
In Past years, Many Security Researchers reported various Oauth vulnerabilities to the Facebook Security team, but if the app traffic is not encrypted, you are not protected from the man-in-the middle attack and the attacker could steal your private information, using 'access token'.
Thus, access token is enough to allow a hacker to do all that the app authorized to do. The vulnerability is not new, it has already been known for a year, but Facebook is still vulnerable to hackers and surveillance specialized agencies like the NSA.
FACBOOK CAN'T FIX IT: The Facebook Security team has acknowledged the vulnerability claimed by Ahmed Elsobky, a penetration tester from Egypt, "We'd actually received an earlier report from another researcher regarding this same issue. In response to that report, we've been working on limiting this behavior when it comes to our official apps, since they're pre-authorized. For other apps, unfortunately, fully preventing this would mean requiring any site integrating with Facebook to use HTTPS, which simply isn't practical for right now."
He demonstrated that 'How to hack a Facebook account by hijacking access token with Man-in-the-Middle attack', as shown:
Facebook apps must be protected from man-in-the middle attacks, and this can be done effectively by using HTTPS to encrypt any traffic that contains sensitive information or authentication credentials...
HOW TO PROTECT YOUR ACCOUNT: If You are a Facebook app developer, you should never send an 'access token' over unencrypted channels and Facebook users should only trust the encrypted apps and use "HTTPS Everywhere" Browser Extension for automated security...
Monday, 17 March 2014
Labels:
Cyber News
# Pakistan Zindabad
Read More
TOYOTA & RENAULT & CHEVROLET Guatemala Hacked
TOYOTA & RENAULT & CHEVROLET Guatemala Hacked
# Hacked By Team Cyber Criminals
# Pakistan Zindabad
http://www.chevrolet.com.gt/
http://www.renault.com.gt/
http://www.toyota.com.gt/
Hacked By Team Cyber Criminals
mirrors;
http://zone-h.com/mirror/id/22028173
http://zone-h.com/mirror/id/22028170
http://zone-h.com/mirror/id/22025495
Pakistani Team..
Labels:
Cyber News
Read More
Yet Another Cyber attack on Iranian Nuclear Facility
TEHRAN, Iran (AP) — Iranian Authorities have discovered another "Code Bomb" in Iran's Heavy water reactor which have been successfully Neutralized before any disaster Occurred .
Asghar Zarean , Senior nuclear security officed at the Atomic Energy Organization of Iran said on saturday"Iran's intelligence agencies were instrumental in uncovering the plot. authorities detected sabotage at the country's heavy water reactor facility and neutralized it before any damage was done."
Iran's Natanz uranium enrichment facility was already target in 2010 by so-called Stuxnet virus that disrupted operation of centrifuges, a key component in nuclear fuel production.
Asghar Zarean Further added Stuxnet and other computer virus attacks are part of a concerted campaign by Israel, the U.S. and their allies to undermine its nuclear program.
Sunday, 16 March 2014
Labels:
Cyber News
Read More
NATO Websites Targeted in Attack Claimed by Ukrainian Hackers
NATO said several of its websites were targeted in a “significant” cyber attack on Saturday that was claimed by Ukrainian hackers in what appeared to be the latest bout of virtual warfare linked to the country’s crisis.
Spokeswoman for the military alliance Oana Lungescu said on Twitter that the websites had been hit by “a significant DDoS (denial of service) attack”, but that it had had “no operational impact”.
Under DDoS attacks, hackers hijack multiple computers to send a flood of data to the target, crippling its computer system.
Lungescu said experts were working to restore normal function but the websites remained down for hours and still could not be accessed at around 0430 GMT on Sunday.
Lungescu did not say who was responsible for the attack, which was claimed by a Ukrainian hacker group called Cyber Berkut, the name given to the feared elite riot police involved in a bloody crackdown on protesters in Kiev.
In a statement on its website www.cyber-berkut.org, the group said it had targeted three NATO websites over what it claimed was the alliance’s interference in Ukraine and support of the “Kiev junta”.
“We will not allow the presence of NATO in our homeland,” said the statement, which could not be independently verified.
Ukraine has been shaken by turmoil that saw a bloody street revolt oust pro-Russian president Viktor Yanukovych in February as anger exploded over his rejection of closer ties with the European Union in favour of Moscow.
Moscow sparked anger after it sent its forces to occupy the majority Russian-speaking Black Sea peninsula of Crimea, where regional authorities declared independence and will hold a referendum on Sunday on whether to leave Ukraine and join Russia.
NATO and its members have spoken out strongly against the vote, which has escalated East-West tensions to their worst point since the Cold War.
The electronic attack is the latest of several that have seen Ukraine tensions hit cyberspace.
On March 8, British-based BAE Systems said dozens of computer networks in Ukraine had been infected by an aggressive new cyber weapon called Snake, which experts said was most likely the work of Russian hackers.
Labels:
Tricks
Read More
How to get avast! Internet Security license for free
How to get avast! Internet Security license for free
Avast, the most trusted antivirus in the world. In business for over 25 years, AVAST is one of the pioneers in the computer security business, with a portfolio covering everything from free antivirus for PC, Mac, and Android. Today, I got a 2 year license(see the above picture) for free from avast by recommending avast to others. You can also get the Premium license key by recommend others. Just follow the below steps to get into the recommendation process. 
Avast Internet Security Features:
Intelligent Antivirus with new DynaGen technology
Anti-malware Protection
Anti-spyware & anti-rootkit
avast! Community IQ
Software Updater maintenance tool
Streaming virus database updates
Browser Cleanup, for tidy web surfing
New user-friendly interface
Enhanced touch screen navigation
Boot-time malware scanning & much more.
Step 02:- After installing, Login or signup for an AVAST account at my.avast.com
Step 04:-Then Promote the copied link on your blog or social media accounts (facebook, twitter etc) and encourage others to use Avast
That’s all, Each successful recommendation gets you closer to a free license of avast! Internet Security.
I hope you’ll enjoy this post 
Labels:
Cyber News
Read More
PTA have decided to block SMS service Of Spammers
PTA (Pakistan telecommunication authority) have decided to block SMS service of those mobile connections which send more than 200 SMS in the duration of 15 minutes, to stop Spam and illegal marketing unwanted SMS messages.
PTA is efforting to stop illegal marketing and unwanted SMS spam for a better and peaceful SMS community in Pakistan.
PTA have said that those mobile connection who will be sending more than 200 SMS within the duration of fifteen minutes will face SMS service blockage.
Then customer will have to contact PTA to request for SMS service restoration. PTA sometimes ask customers for sending letter also to the PTA headquarters address. Customer’s SMS service will be restored but if customer repeats, his SMS service will be blocked permanently
Subscribe to:
Comments
(
Atom
)